Pyphisher termux tool to hack social media account
7 min read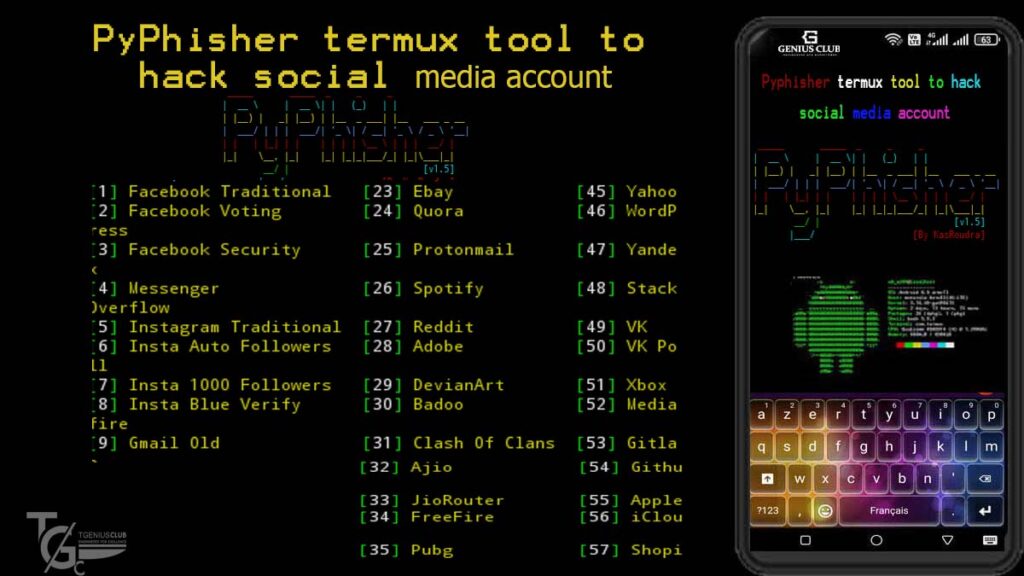
Social media accounts are prime targets for hackers seeking to steal sensitive data or spread malicious content. Social engineering attacks like phishing are commonly used to obtain login credentials for user accounts. Pyphisher is a powerful tool for carrying out phishing attacks on social media platforms.
The tool is especially potent when used in combination with Termux, an Android terminal emulator app. In this article, we will outline what Pyphisher is, how it works, and the steps involved in using it for social media hacking.
Additionally, we will discuss the legal implications of using Pyphisher for hacking and measures that can be taken to protect against such attacks.
Well, nowadays, social media accounts have become the target of some bad guys or script kiddies on the internet. They try to hack social media accounts for different reasons like for money, impressing others, or other reasons. Before discussing Pyphisher we are going to discuss how they do to hack social media accounts.
Pyphisher is in the same category as Zphisher, Anonphisher, Mrphish, and other social media hacking tools.
Table of contents
- How do hackers hack social media accounts?
- Introduction to Pyphisher termux tool
- Understanding social engineering attacks
- How Pyphisher can be used to hack social media accounts
- Step-by-step guide on using Pyphisher for social media hacking
- the installation process of Pyphisher
- Legal consequences of using Pyphisher for hacking
- Conclusion and future implications of Pyphisher termux tool in social engineering
- Disclaimer
How do hackers hack social media accounts?
Even if Facebook is more secure, black hackers use some techniques to hack Facebook accounts. We can mention phishing, keylogging, Trojans/backdoors, Sniffing, Social Engineering, and Sessions Hijacking …
These techniques are not the only ones to use. But it depends on the attackers, some can develop their own scripts to perform their attacks and others can use other developers’ scripts. We are going to discuss phishing techniques as Pyphisher is a phishing tool.
phishing

Phishing is one of the easiest ways to trick users into giving out their login credentials. All an attacker does is set up a webpage similar in design to the victim’s homepage. Then, he attaches a server-side script to track the username and password entered and stores it in a log.
After the attacker finished setting up the server-side then he can send the link by using some attractive words to the victim. The attacker can combine both phishing and social engineering attacks to trick the victim.
The attacker will be waiting for the victim to log in to that fake page and get the information entered and “boom” the account will be hacked.
However, some social media started detecting and blocking phishing links. But there is some other way to send a phishing link without getting blocked.
Introduction to Pyphisher termux tool
What is Pyphisher?
Pyphisher is a powerful and popular social engineering tool used for phishing and hacking social media accounts. It is designed to deceive users into giving away their sensitive information such as usernames, passwords, credit card details, and personal identification numbers (PINs) by luring them to fake login pages.
Pyphisher is an excellent tool for penetration testers, cybersecurity experts, and ethical hackers. It includes popular websites like Facebook, Twitter, Instagram, GitHub, Reddit, Gmail, and many others
What is Termux?
Termux is a powerful terminal emulator and Linux environment for Android devices. It enables users to access a full Linux distribution on their Android smartphone or tablet.
Termux provides an extensive package repository with over 3700 packages and a powerful terminal interface that allows users to execute commands, install applications, and access files in a Linux environment.
Understanding social engineering attacks
What is social engineering?
Social engineering is a psychological technique used to manipulate people into divulging sensitive information, committing fraudulent acts, or compromising their security.
Also, It uses various tactics such as deception, impersonation, and intimidation to exploit human weaknesses and gain access to sensitive information or systems.
How Pyphisher can be used to hack social media accounts
Features of Pyphisher tool
Pyphisher tool comes with many features that make it a powerful and effective social engineering tool. These features include a user-friendly interface, customizable phishing templates, and support for multiple social media platforms, among others.
How does Pyphisher work?
Pyphisher works by cloning the login page of a targeted social media platform, such as Facebook, Instagram, or Twitter. It then uses this fake login page to trick the victim into entering their login credentials. Once the victim submits their credentials, Pyphisher captures and stores them for later use.
Pyphisher also provides multiple phishing templates that mimic the social media platform’s login page, making it easier to deceive the victim.
Pyphisher requirements
Well, as you might know, most termux tools required some dependencies before being installed or used. We are going to see what are Pyphisher dependencies and how to get them so that we avoid getting errors during installation.
Python(3)PHPCurlUnzipWget- 90MB storage (All files from git clone)
- 60MB storage (Direct run script without git clone)
Well, you may find that you have some of these dependencies installed on your termux. But if you don’t have them, don’t worry, we will discuss how to get them.
Step-by-step guide on using Pyphisher for social media hacking
Installation of dependencies
Now we can start installing some dependencies before the installation step, but if you have these dependencies you can go to the next step which is about the installation. But before installing any dependency, start by updating and upgrading the termux repository.

Installation of Python 3
The installation of Python on termux is simple to do, just by using the command:
pkg install python
Installation of PHP
Then, we can proceed to install PHP after we have done the Python installation.
pkg install PHP
Installation of curl and wget
We can install curl and wget by using the command:
pkg install curl wget -yAlso, we can’t forget to install git because to get Pyphisher from GitHub we will use the git command, only use the command if you don’t have git installed:
pkg install git 
Now, as we have seen how we can install all dependencies we can now continue with the installation.
the installation process of Pyphisher
By using the command git we are going to get Pyphisher from Github and start the installation.
git clone https://github.com/KasRoudra/PyPhisher
Then, after we have got the Pyphisher folder into our termux we can now navigate into Pyphisher folder using the command: cd PyPhisher. And then to run the Pyphisher script, we use the command:
python3 pyphisher.pyWhen you run the script the installation of Ngrok and Cloudflare will start.

And then after the installation will be finished we will now be ready to use Pyphisher.

Selecting a social media platform to target
Pyphisher supports numerous social media platforms, including Facebook, Instagram, Twitter, and many others. Choose the social media platform you want to target and select the appropriate phishing template from Pyphisher’s dashboard.
How to protect against social engineering attacks
The first line of defense against social engineering attacks is to be aware and suspicious of any communication that seems unusual or unexpected. Be cautious of unsolicited emails, text messages, phone calls, or social media messages, especially if they ask for personal or sensitive information. Always verify the identity of the sender before responding or clicking on any links.
Additionally, make sure to keep your software updated and use strong passwords that are unique for each account. Consider enabling two-factor authentication for an extra layer of security. Lastly, use reputable security software that can detect and block social engineering attacks or phishing attempts.
Recognizing and reporting phishing attempts
Phishing is a common form of social engineering attack that involves tricking users into providing sensitive information such as usernames, passwords, or credit card details. To recognize phishing attempts, look for warning signs such as suspicious links or attachments, misspellings, or urgent requests for information.
If you encounter a phishing attempt, do not respond or provide any information. Instead, report the attempt to the relevant authorities or the company being impersonated.
Most companies have a dedicated email address or form for reporting phishing attempts. Reporting phishing attempts helps companies to take appropriate measures to protect their users and prevent future attacks.
Legal consequences of using Pyphisher for hacking
Using Pyphisher for hacking social media accounts is illegal and can result in serious legal consequences. It is important to understand the legal implications of hacking and the potential consequences of using tools like Pyphisher for illegal purposes.
Legal Implications of hacking social media accounts
Hacking social media accounts without the owner’s permission is a violation of the Computer Fraud and Abuse Act (CFAA) and can result in criminal charges.
Depending on the severity of the offense, the perpetrator can face fines, imprisonment, or both. Hacking can also result in civil lawsuits and damage to the victim’s reputation and privacy.
Conclusion and future implications of Pyphisher termux tool in social engineering
Social engineering attacks are a growing threat, and tools like Pyphisher can make them even more effective. It is important to remain vigilant and take necessary precautions to protect against such attacks.
Summary of Pyphisher tool and its use in social engineering attacks
Pyphisher is a powerful tool that can be used to conduct social engineering attacks and hack social media accounts. However, the use of Pyphisher for illegal purposes can lead to severe legal consequences.
Disclaimer
This article is for educational purposes. Here it demonstrates how phishing works. If anybody wants to gain unauthorized access to someone’s social media, he/she may try out this at his/her own risk.
You have your own responsibilities, and you are liable for any damage or violation of laws by this tool. The author is not responsible for any misuse of PyPhisher!







i install it in termux but it doesn’t open when i writing this “python3 pyphisher.py”