ChatGPT-4 et l’Avenir de l’IA Conversationnelle : Comprendre l’Évolution et ses Applications Pratiques
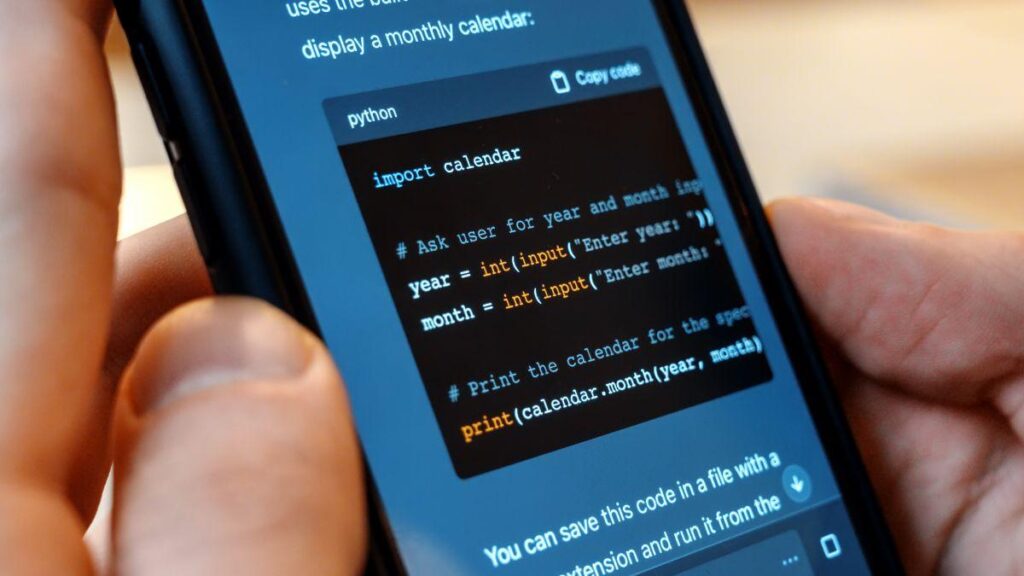
ChatGPT-4 n’est pas seulement un outil pour les curieux de la technologie. Ses applications pratiques sont vastes et diversifiées, touchant plusieurs secteurs d’activité.